About a year ago, I developed a WordPress extension called WP Login Attempt Log. All it does is log every incorrect login attempt to your WordPress page and display some graphics and a way to search the logs. It logs the username, the password, the IP address and also the user agent, e.g. the browser version.
Observation number 1: attacks come and go
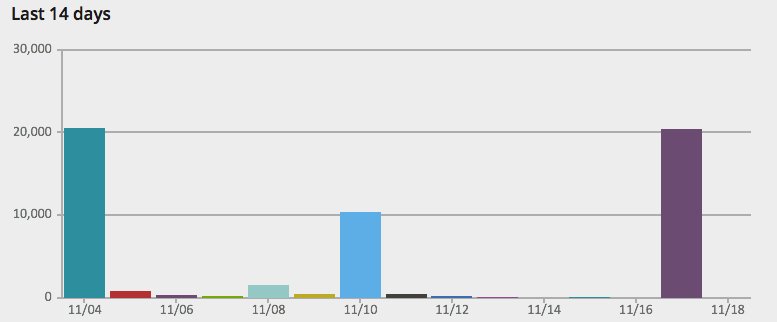
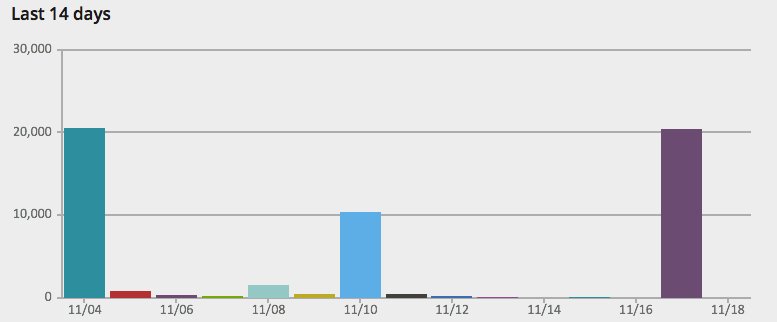
Screenshot of login attempts from the past 2 weeks, from the plugin
One thing that is striking about this graph is how much the number of attacks differ per day. Some day I will get tens of thousands of attempts, on other days I will get under 100. On average, though, I get about 2200 attempts per day, 15,000 per week and 60,000 per month. It suggests that my site is part of a rotation, or maybe that someone really wants to hack my blog on mondays.
Observation number 2: passwords are tried multiple times
All in all, there's about 36,000 unique passwords that have been used to brute-force my WordPress blog. From the total number of around 360,000 attacks, each password must is used on average of 10 times. But of course, some are used more than others, as you can see in the table below.
What's interesting is that there's not a larger amount of different passwords. From the large password database leaks the past few years – we're talking tens of millions – one could expect the amount of different passwords more closely matching the number of total attempts.
Of course, there might also just be 10 different people out to hack my blog, and they all have the same password list. :-)
Observation number 3: the most common password is "admin"
An empty password was tried around 5,300 times. Here's a list of the most used passwords, along with how many times they were used:
| Attempts |
Password |
| 5314 |
(blank) |
| 523 |
admin |
| 284 |
password |
| 269 |
123456 |
| 233 |
admin123 |
| 230 |
12345 |
| 215 |
123123 |
| 213 |
12345678 |
| 207 |
1234 |
| 205 |
admin1 |
| 203 |
internet |
| 202 |
pass |
| 201 |
qwerty |
| 198 |
mercedes |
| 194 |
abc123 |
| 191 |
123456789 |
| 191 |
111111 |
| 191 |
password1 |
| 190 |
freedom |
| 190 |
eminem |
| 190 |
cheese |
| 187 |
test |
| 187 |
1234567 |
| 186 |
sandra |
| 184 |
123 |
| 182 |
metallica |
| 181 |
simonfredsted |
| 180 |
friends |
| 179 |
jeremy |
| 178 |
1qaz2wsx |
| 176 |
administrator |
This is not a list of recommended passwords. :-) Definitely don't use any of those.
Observation number 4: 100 IP addresses account for 83% of the attempts
The top 1 IP address that have tried hacking my blog, 54.215.171.123, originates from a location you wouldn't suspect: Amazon. That IP has tried to attack my blog a whopping 45,000 times, 4 times that of the second IP on the list.
I took the top 25 offenders and did a WHOIS on them. I guess if you're looking for a server company to do your WordPress hacking, here you go:
| Attempts |
IP Address |
ISP |
Country Code |
| 45465 |
54.215.171.123 |
Amazon Technologies |
US |
| 15287 |
63.237.52.153 |
CenturyLink |
US |
| 10842 |
123.30.212.140 |
VDC |
VN |
| 10425 |
185.4.31.190 |
Green Web Samaneh Novin Co |
IR |
| 10423 |
95.0.223.134 |
Turk Telekom |
TR |
| 10048 |
46.32.252.123 |
Webfusion Internet Solutions |
GB |
| 10040 |
94.23.203.18 |
OVH SAS |
FR |
| 10040 |
46.4.38.83 |
Hetzner Online AG |
DE |
| 10040 |
108.168.129.26 |
iub.net |
US |
| 10040 |
193.219.50.2 |
Kaunas University of Technology |
LT |
| 10036 |
84.95.255.154 |
012 Smile Communications |
IL |
| 10035 |
80.91.189.22 |
Private Joint Stock Company datagroup |
UA |
| 10030 |
94.230.240.23 |
Joint Stock Company TYVASVIAZINFORM |
RU |
| 10030 |
123.30.187.149 |
VDC |
VN |
| 10029 |
89.207.106.19 |
Amt Services srl |
IT |
| 9328 |
67.222.98.36 |
IHNetworks, LLC |
US |
| 9327 |
85.95.237.218 |
Inetmar internet Hizmetleri San. Tic. Ltd. Sti |
TR |
| 9327 |
62.75.238.104 |
PlusServer AG |
DE |
| 9326 |
5.39.8.195 |
OVH SAS |
FR |
| 9326 |
5.135.206.157 |
OVH SAS |
FR |
| 9208 |
211.25.228.71 |
TIME dotCom Berhad |
MY |
| 9168 |
176.31.115.184 |
OVH SAS |
FR |
| 8804 |
78.137.113.44 |
UKfastnet Ltd |
GB |
| 8201 |
134.255.230.21 |
INTERWERK - Rotorfly Europa GmbH & Co. KG |
DE |
| 7598 |
5.199.192.70 |
K Telecom |
RU |
| 6952 |
85.195.91.10 |
velia.net INternetdienste GmbH |
DE |
| 5231 |
67.222.10.33 |
PrivateSystems Networks |
US |
| 3546 |
5.248.87.146 |
Kyivstar PJSC |
UA |
| 3202 |
78.46.11.250 |
Hetzner Online AG |
DE |
| 2099 |
93.45.151.167 |
Fastweb |
IT |
| 1940 |
92.222.16.54 |
OVH SAS |
FR |
Another interesting thing about this is is the amount of IPs hovering at around 10,000 attempts. It seems like there's a limit where the attacker gave up, moved on to the next target. Maybe all these are a part of a single botnet, and each machine in it is only allowed to attack 10,000 times. Who knows.
Observation number 5: protect yourself by using an unique username
WordPress hackers are really sure that you'll use a pretty standard username, or at least something to do with the name of your blog. A total of just 165 different usernames were tried, compared to the tens of thousands of passwords.
Therefore my final takeaway is to choose an obscure username as well as an obscure password. There's only 11 usernames that have been used more than a hundred times. This was kind of surprising to me.
| Attempts |
Username |
| 164360 |
admin |
| 119043 |
simon |
| 15983 |
administrator |
| 10787 |
test |
| 10429 |
adm |
| 10416 |
user |
| 9871 |
user2 |
| 9253 |
tester |
| 8147 |
support |
| 1818 |
simonfredsted |
| 189 |
simo |
| 57 |
root |
| 57 |
login |
| 56 |
admin1 |
| 3 |
qwerty |
| 3 |
[email protected] |
| 3 |
simonfredsted.com |
| 2 |
aaa |
That's a lotta attacks, what do I have to fear?
WordPress blogs is one of the most targeted platforms for hackers, many sites use it, from big news organisations to small blogs like this one. If someone can get a login and start fiddling with your links, they can boost traffic to their own viagra peddling sites.
But, as long as you keep your software updated (WordPress makes this very, very easy) and keep the following two rules in mind, you're totally safe.
Bottom line: Set a lengthy password consisting of random characters, letters and digits, and use a username that's not a part of your name, site URL or "admin". Maybe just use some random letters, your password manager will remember it after all.
If you do those two things, there's nothing to worry about.
If you have your own take on this data, or think I've misinterpreted something, feel free to leave a comment below or on Hacker News – I'd love to hear your thoughts.
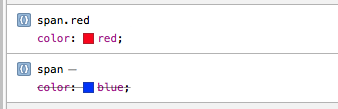
 Strikethroughs in the Safari Web Inspector styles? Here’s why
Strikethroughs in the Safari Web Inspector styles? Here’s why